Find Vulnerabilities On Your Network and/or Website
AVDS is a network penetration testing and vulnerability detection appliance for networks with as many as 200,000 nodes. It performs an in-depth inspection for security weaknesses that can replace expensive penetration testing systems.
With each scan it will automatically find new equipment and services and add them to the inspection schedule. It then tests every node based on its characteristics and reports its responses to reveal security issues in equipment, operating systems and applications. You set the IP range to investigate and in a matter of hours and with no network downtime or interruption of services, AVDS will generate detailed reports specifying network security weaknesses.
The database of tests is updated daily with the most recently discovered security vulnerabilities. The AVDS database includes over 10,000 known vulnerabilities and the updates include discoveries by our own team and those discovered by corporate and private security teams around the world.
Manual penetration tests and vulnerability assessment is expensive and infrequently done. The software can be time consuming to set up and operate, plagued by high false positive rates and cause network resource issues. AVDS solves these problems:
The frequency and increasing severity of today's security threats are forcing companies to:
Selecting, purchasing, deploying and managing a vulnerability detection tool that is reliable and matched to your organization's needs is not an easy task!
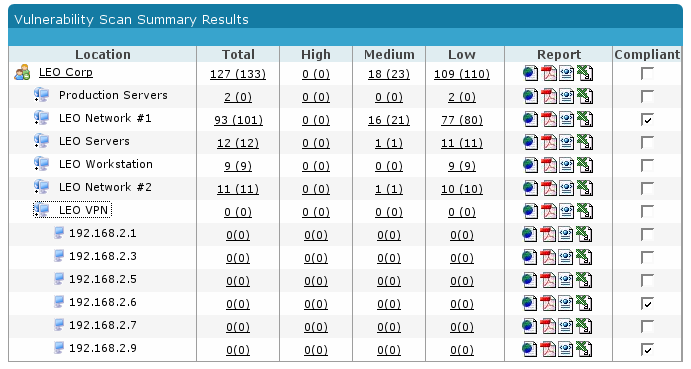
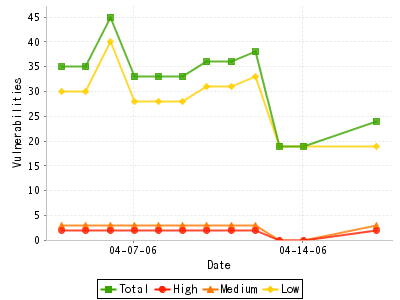
AVDS conducts automated vulnerability scans daily, weekly or monthly, or on ad-hoc basis. It records results and generates vulnerability trends for your entire WAN a LAN or single IP address. With three levels of reporting, each business unit can receive a report on it's own network and local results can be combined into a company wide picture.
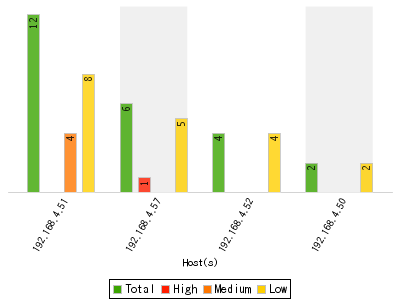
Pin point your most vulnerable IPs by either a ranked list or graph. Use AVDS to identify exactly which patches, solutions and workarounds to install. Re-scan networks and hosts after solutions have been implemented to verify and document compliance and remediation.
Each AVDS report contains the exact solutions to repair the problems found. This in-depth information shows how to fix and improve the security of your network, both as whole and for each of the devices in it. The recommended solutions include device specific information as well as custom tailored solutions for your environment.
Whether your network is as small as one LAN or involves hundreds of business units separated by firewalls, or even continents, all testing and report generation can be managed and controlled from one location with individual reports being automatically delivered to each business unit. Multiple scanners can be used to overcome bandwidth restrictions, firewall segmentations or to load balance and provide fault tolerance.
Reports can be calendared and their delivery automated. Report formats available include PDF, HTML, CSV and XLS. In addition AVDS can deliver vulnerability scan results to any SIEM, ticketing, project management or other data collection application. Reports adhere to standards set by Basel II, CVE, CVSS, ISO and ITU.
AVDS is also available as a small business solution that can deliver the most frequently used reports. This system (Stand Alone System - or SAS) uses the same VA engine and library of vulnerabilities as the Management System but is ideal for businesses who are just getting started on vulnerability assessment or who have simple networks and modest budgets.
The AVDS standard report provides a comprehensive analysis of all vulnerabilities found. An Executive Summary section shows an overall summary, illustrated by charts and graphs to allow quick assessment of the risks found in the scan. The Vulnerabilities section shows the technical information for every vulnerability found, including a short summary, severity, possible impact, recommended solution and links to more information. The technical report is a powerful tool for network administrators, security officers and IT managers to evaluate network security.
This unique reporting feature presents only the changes from any previous scan. New vulnerabilities, open ports, new services or new/removed hosts will appear, as well as a summary of the problems that were fixed. This crucial management tool immediately highlights potential risks, unauthorized activity or security-related network actions.
A graphical illustration showing the changes of risk level over time and the progress toward the implementation of a security policy. The vulnerabilities section of the change or trend reports will tell the administrator what are the new issues that need to be dealt with.
Designed for senior IT executives this report provides modest graphics with enough supporting detail to assist in decision making.
This report provides more graphics and less detail - ideal for presentation to non-technical decision makers.
Create special reports using filters and search parameters to view vulnerability results on a select set of hosts, an operating system, an application, a risk type, a risk rating or any combination.
Beyond Security is an Approved Scanning Vendor and PCI compliance reports on external IPs and URLs are done by PCI trained staff on request and are included at no extra price with every installed system.
Lists status of tickets created in the AVDS ticketing system.
A comprehensive report of all network assets discovered within each scan range including asset value, OS, NetBIOS, DNS and MAC address.
Large enterprises often need vulnerability reports that may combine selected hosts from several different scans.
This report is often used to clean up a network that has not previously received routine vulnerability assessment scanning. In some cases handling all instances of one vulnerability is more efficient than handling all vulnerabilities on one host.
Reports suitable for reporting HIPAA and SOX compliance are also available.
Call 212-684-5553 or click here learn more and schedule a consultation with our experts.

Keep the bad guys off your network, speed up Internet access and improve your business continuity profile with this amazing new service.

More and more, malware is being delivered from rogue websites visited by people on your network. Protect your network from these dangerous threats.

Our service blocks 99 percent of spam and viruses, keeping your inbox clean and your network safe.

Perform in-depth inspection for security weaknesses that can replace expensive penetration testing.